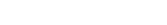
Too Many
DNS Providers? Why DNS Management Becomes Chaos at Scale
There is a strange pattern in modern infrastructure:
some of the most business-critical systems receive attention
There is a strange pattern in modern infrastructure: some of the most business-critical systems receive attention only after they fail.
DNS is one of them.
When DNS works, nobody talks about it. Applications load, APIs respond, email flows, certificates validate, and traffic reaches the right destination. It feels invisible. But when DNS breaks, it can disrupt everything at once.
A website becomes unreachable. A production API starts failing. SSL certificate validation stops working. Traffic routes to the wrong environment. A migration stalls because records were updated in one provider but forgotten in another. Suddenly, an area of infrastructure many teams considered “simple” becomes the center of an urgent incident.
For growing organizations, the real challenge is rarely DNS itself. It is DNS management.
Modern businesses often accumulate domains, subdomains, cloud accounts, environments, acquisitions, regional deployments, and multiple DNS providers over time. What began as a few records in one console turns into a fragmented operational surface spread across platforms such as Route53, Cloudflare, Azure DNS, and others.
That is where complexity begins to multiply.
This article explores why DNS management becomes chaotic at scale, the risks created by fragmented operations, and how DevOpsArk helps organizations bring control, visibility, and consistency to multi-provider DNS environments.
DNS Was Never Designed to Be a Daily Operational Headache
At its core, DNS is straightforward. It translates names into destinations. Humans use readable domains, systems use IP addresses, and DNS connects the two.
The challenge is not the concept. The challenge is how deeply DNS is woven into modern operations.
DNS affects:
- Public websites
- Internal services
- APIs
- Load balancers
- SSL certificate validation
- Email delivery
- Disaster recovery failover
- Regional traffic routing
- Environment separation
- Vendor integrations
That means DNS changes are rarely isolated. A single record update can affect customers, security controls, availability, and deployment timelines simultaneously.
When organizations scale, DNS stops being a simple configuration task and becomes an operational discipline.
How DNS Chaos Usually Begins
Few companies intentionally create a messy DNS environment. It usually happens gradually.
A startup may begin with one domain and one provider. Later, a new product launches. A separate team chooses another provider. A cloud migration introduces Route53. Security adopts Cloudflare. A regional team uses Azure DNS. Marketing buys new domains through another registrar. Acquisitions bring inherited zones and undocumented records.
Each decision may be reasonable in isolation.
Together, they create fragmentation.
Now the organization has:
- Multiple consoles
- Different ownership models
- Inconsistent naming standards
- Duplicate records
- Unknown dependencies
- Broad admin access
- Manual processes for urgent changes
- No shared operational view
This is not unusual. It is the natural result of growth without a unified DNS operating model.
Why Multi-Provider DNS Becomes Risky
Using multiple providers is not inherently wrong. Many businesses have valid reasons for it.
The problem appears when multi-provider strategy lacks governance.
No Single Source of Truth
Teams often do not know where the authoritative record lives. A change is made in one provider while another environment still points elsewhere. During incidents, confusion increases because everyone is checking different systems.
Human Error During Changes
DNS updates are often small but high-impact. A typo, wrong target, incorrect TTL, or accidental deletion can create production issues immediately.
As the number of providers grows, so does the chance of mistakes.
Slower Incident Response
When traffic is failing, teams need speed. If responders must first determine which provider controls which zone, valuable time is lost.
Security and Access Sprawl
Different platforms often mean different user accounts, permissions, and audit trails. Over time, access becomes harder to govern consistently.
Operational Drift
Naming conventions, TTL policies, failover patterns, and documentation can diverge between teams and environments. That drift creates hidden complexity.
Why DNS Problems Feel Bigger Than They Look
A minor DNS change can trigger outsized business impact.
That is because DNS sits in front of many critical systems. If it fails, healthy applications may appear broken simply because traffic cannot reach them correctly.
A service may be running perfectly while customers experience downtime. An API may be healthy while integrations fail. A migration may be technically complete while users still hit the old endpoint.
This is why DNS incidents often feel confusing at first. The problem is not always in the application layer. It may be in the path users take to reach it.
Why Growing Teams Need Better DNS Operations
As organizations mature, DNS changes become more frequent and more sensitive.
New products need subdomains. Staging and production environments must stay separate. Certificate automation depends on correct records. Cloud migrations require routing changes. Regional expansions need traffic control. Security teams need stronger governance. Leadership expects fewer avoidable outages.
At that point, managing DNS through scattered consoles and tribal knowledge stops scaling.
The issue is not whether teams are skilled. It is whether the operating model supports the pace and complexity of the business.
What Good DNS Management Looks Like
Strong DNS operations do not mean eliminating every provider. They mean making multi-provider environments manageable.
Mature teams aim for:
- Central visibility across zones and providers
- Clear ownership of domains and records
- Controlled access based on responsibility
- Faster, safer record changes
- Consistent standards across environments
- Better auditability
- Reduced dependency on tribal knowledge
- Faster incident response
The goal is simple: make DNS predictable.
How DevOpsArk Helps Simplify DNS at Scale
DevOpsArk helps organizations manage DNS as an operational capability instead of a scattered collection of provider consoles.
Rather than forcing teams to jump between platforms for everyday changes, troubleshooting, and governance, DevOpsArk helps create a more centralized and consistent DNS management experience across providers such as Route53, Cloudflare, Azure DNS, and others.
That shift matters because most DNS pain is not caused by the protocol itself. It is caused by fragmented operations.
Centralized Multi-Provider DNS Management
When records are spread across platforms, visibility suffers.
DevOpsArk helps teams manage DNS across multiple providers through a more unified model, reducing the friction of switching between tools and improving clarity across environments.
This makes day-to-day operations simpler and incidents easier to navigate.
Faster and Safer Record Changes
DNS updates often happen during launches, migrations, failovers, and urgent fixes.
In those moments, teams need confidence.
DevOpsArk helps streamline DNS changes so updates can happen with better control and less operational overhead, reducing the chance of avoidable mistakes.
Better Governance and Access Control
As more people interact with DNS, governance becomes essential.
DevOpsArk helps organizations improve control over who can manage records and domains, making DNS operations more secure and easier to govern at scale.
Reduced Operational Drift
Consistency matters.
DevOpsArk helps teams bring more standardization to DNS workflows across environments and providers, reducing the long-term drift that often accumulates in growing organizations.
Practical Example
Consider a company operating customer workloads across multiple clouds.
Their public website uses one DNS provider. Internal services use another. A new region was added last year. Security introduced additional controls. Several teams can edit records. Documentation is incomplete.
During a migration, traffic begins routing incorrectly.
The application team checks infrastructure. Networking checks load balancers. Security checks firewalls. Eventually, the issue is traced to a DNS change made in one platform while another record remained outdated elsewhere.
The outage was not caused by weak engineering talent.
It was caused by fragmented operations.
Now imagine the same company using DevOpsArk to manage DNS with stronger visibility, clearer ownership, and a more unified change process.
The migration still requires coordination. But it is faster, clearer, and far less chaotic.
That difference is operational maturity.
Signs Your DNS Model Needs an Upgrade
Many organizations can spot DNS maturity gaps before a major outage happens.
Common signals include:
- Multiple providers with no shared view
- Nobody knows who owns certain zones
- DNS changes require asking around internally
- Record mistakes have caused incidents before
- Access is broader than it should be
- Documentation is outdated
- Teams use inconsistent standards
- Troubleshooting starts with guessing where records live
These are signs that the environment has grown beyond its current model.
Final Thoughts
DNS rarely gets credit when systems run smoothly, but it quickly becomes visible when something goes wrong.
For modern organizations, the challenge is no longer simply hosting records. It is managing DNS across multiple providers, teams, environments, and business demands without creating unnecessary risk.
DevOpsArk helps organizations bring order to that complexity through centralized multi-provider DNS management, better governance, stronger visibility, and more consistent operations.
Because at scale, DNS should be infrastructure you trust — not infrastructure you fear during every change.
Recent Posts
- Too Many DNS Providers? Why DNS Management Becomes Chaos at Scale
- When Recovery Fails, Backups Don’t Matter: Why Modern Backup Strategies Need a Rethink
- Secrets in Spreadsheets? Why Credential Management Still Breaks Modern Teams
- SSH Access Chaos: Why Public Server Access Is a Security Nightmare in 2026 (And How Modern Teams Fix It)
- SSL Expired Again? Why Certificate Management Still Breaks Businesses in 2026 (And How to Finally Fix It)