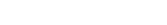
Secrets in
Spreadsheets? Why Credential Management Still Breaks Modern Teams
Secrets management remains one of the most overlooked operational
challenges in modern engineering teams. It affects security,
Secrets management remains one of the most overlooked operational challenges in modern engineering teams. It affects security, release velocity, compliance, and the ability to scale infrastructure safely.
There is a familiar scene that plays out in far more companies than anyone likes to admit.
A release is scheduled for the evening. Someone on the team needs database access. Another person needs an API token for a third-party integration. A contractor requires temporary credentials to validate a deployment. Nobody wants to delay the release, so the fastest solution wins. A password is dropped into chat. A spreadsheet link is shared. An old .env file is forwarded. Someone says, “We’ll clean this up later.”
Later rarely comes.
Weeks pass. Then months. More systems are added, more engineers join, more vendors need access, more automation is built. The temporary workaround quietly becomes the operating model. By the time anyone questions it, the organization is relying on a fragile web of shared passwords, copied tokens, undocumented credentials, and access paths that nobody fully understands.
This is how credential management breaks modern teams. Not through dramatic mistakes, but through small conveniences repeated over time.
And in 2026, when infrastructure is distributed, cloud-native, and deeply interconnected, that cost is higher than ever.
The Problem Is Bigger Than Password Storage
When people hear the phrase secrets management, they often think only about storing passwords securely. That is part of the picture, but it is a small part.
Modern systems run on machine-to-machine trust. Applications authenticate to databases. Pipelines authenticate to cloud platforms. Monitoring tools authenticate to APIs. Containers pull images from private registries. Internal services exchange tokens. Deployment systems connect to Kubernetes clusters. Every one of those interactions depends on credentials of some kind.
Those credentials are the connective tissue of modern infrastructure.
If source code is the logic of a system, secrets are what allow that logic to interact with the world.
Which means poor credential management is not a side issue. It affects security, reliability, delivery speed, compliance, and operational confidence all at once.
Why Smart Teams Still End Up With Credential Chaos
Most teams do not choose bad security practices deliberately. They inherit them gradually.
A startup moving quickly may begin with a few shared credentials because there are only three engineers. That feels efficient. A second environment is added, then a staging cluster, then a customer-facing integration, then a new cloud account. Team size doubles. Contractors are onboarded. A CI/CD pipeline is introduced. A security review happens. A new product launches.
The credential footprint expands faster than the process around it.
This is where many organizations get stuck. Their engineering maturity grows, but their credential model remains tied to an earlier stage of the company.
The result is a modern platform built on outdated trust workflows.
The Spreadsheet Problem Is Not Really About Spreadsheets
Spreadsheets have become a symbol of bad secrets management, but the real issue is not the file format.
The issue is what spreadsheets represent:
- No central ownership
- No reliable audit trail
- No controlled lifecycle
- No clear rotation process
- No confidence in what is still valid
- No easy way to limit access precisely
- No separation between temporary and critical credentials
The spreadsheet usually starts as a convenience tool. Over time, it becomes a risk registry disguised as documentation.
And spreadsheets are only one example.
The same pattern appears in:
- Shared Notion pages
- Internal wikis
- Password manager folders with broad access
- Chat threads
- CI variables nobody reviews
- Old deployment scripts
- Personal notes saved locally
- .env files copied between teams
The medium changes. The underlying problem does not.
How Credential Sprawl Hurts Engineering Teams
Security teams often frame secrets management as a risk conversation, and they are right. But engineers experience the problem operationally long before they experience it as a breach.
That is why this issue matters across the entire business.
Releases Slow Down for Avoidable Reasons
Anyone who has worked on a pressured deployment has seen this happen.
The build is ready. Validation is complete. Then someone realizes the production token is outdated, the new environment variable was never added, or the required credential is known only by one person who is currently unavailable.
The release pauses not because of code quality, but because credentials are disorganized.
Debugging Gets Harder
When systems fail, teams need confidence in the environment. If authentication errors might be caused by stale tokens, mismatched secrets, or undocumented changes, diagnosis becomes slower and more frustrating.
Onboarding Takes Too Long
A new engineer joins. They need access to tools, environments, dashboards, and deployment systems. Instead of a clean provisioning flow, they receive links, old notes, shared passwords, and tribal guidance.
This is inefficient and risky at the same time.
Offboarding Is Uncomfortable
When someone leaves the organization, leadership should be confident that access has been removed cleanly. In many environments, that confidence does not exist.
There is uncertainty around what credentials were shared informally, copied locally, or reused elsewhere.
The Security Risk Is Real — and Often Invisible
Credential-related incidents are dangerous because they can remain invisible for long periods.
Unlike a crashed service or failed deployment, leaked or overexposed credentials do not always announce themselves immediately. A token copied to the wrong place may still work for months. A former contractor’s access may remain active unnoticed. A cloud key stored in an old script may be discovered later by someone who should never have had it.
This creates a category of risk that grows quietly.
And because secrets grant legitimate access, misuse can look like normal activity unless governance and visibility are strong.
That is why modern security programs increasingly focus on identity, privilege, and secrets hygiene. Attackers do not always need to break in if credentials are already available.
Why Rotation Is Harder Than It Sounds
Many companies know they should rotate secrets regularly. Few do it consistently.
The reason is simple: in real systems, credentials are connected to many dependencies.
Changing one database password may require updates in:
- Application configs
- CI/CD pipelines
- Backup jobs
- Monitoring tools
- Analytics connectors
- Internal admin tools
- Disaster recovery scripts
If teams lack confidence in where a secret is used, they avoid changing it until they are forced to.
That creates a dangerous cycle. Credentials stay unchanged because rotation feels risky. Rotation becomes riskier because credentials stay unchanged.
What Good Credential Management Looks Like
Strong secrets management is not about making engineers jump through unnecessary hoops. It is about reducing chaos while improving control.
In healthy environments, teams know:
- What secrets exist
- Where they are used
- Who owns them
- Who can access them
- How they are updated
- How they are reviewed
- How they are rotated
- How they are retired
This clarity has real operational value.
Releases move faster because dependencies are managed. Audits become easier because evidence exists. Incidents become simpler because ownership is clear. Teams spend less time hunting for credentials and more time building useful systems.
How DevOpsArk Solves the Problem
DevOpsArk approaches secrets management as part of the broader operating model of modern engineering teams.
Instead of treating credentials as scattered artifacts stored across unrelated systems, DevOpsArk helps organizations centralize how secrets are governed, accessed, and managed across environments.
That shift matters because most credential problems are not caused by weak encryption. They are caused by weak operations.
A Central Place for Sensitive Credentials
When teams rely on multiple storage locations, confusion is inevitable.
DevOpsArk provides a unified secrets management layer so organizations can reduce fragmentation and gain clearer visibility into critical credentials.
That means fewer hidden dependencies, fewer duplicated secrets, and fewer situations where nobody knows the current source of truth.
Access Based on Responsibility
Not every developer needs production credentials. Not every contractor needs long-term access. Not every system should see every secret.
DevOpsArk helps organizations align access with real responsibilities, reducing unnecessary privilege while keeping legitimate work efficient.
This improves both security and team productivity.
Better Governance Without Slowing Teams Down
Governance often fails when it feels like bureaucracy.
The goal should be simple, predictable workflows that help teams work safely without adding friction to every task.
DevOpsArk helps standardize credential handling across engineering, operations, and security teams so access processes become clearer and less dependent on tribal knowledge.
Integration With Existing Secret Platforms
Many companies already use tools such as HashiCorp Vault or AWS Secrets Manager. Replacing everything overnight is rarely practical.
DevOpsArk supports integration with existing platforms, allowing teams to improve governance and operational consistency while preserving prior investments.
Easier Lifecycle Management
Secrets should not live forever.
DevOpsArk helps teams create healthier lifecycle practices around updates, reviews, ownership, and controlled changes across environments, making rotation and governance more manageable over time.
A Practical Before-and-After Example
Consider a growing SaaS company with three products, multiple environments, and a hybrid engineering team.
Before
Credentials exist in several places:
- Shared spreadsheet for vendor accounts
- CI/CD variables created by different teams
- Old AWS keys in scripts
- Database passwords known by only two people
- Slack messages used during urgent releases
- No consistent ownership model
Every audit requires manual cleanup. New hires depend on internal folklore. Releases occasionally stall over missing access.
After
The company adopts a centralized secrets operating model through DevOpsArk.
Now they have:
- Clearer ownership of credentials
- Controlled access based on role
- Better visibility across environments
- Cleaner onboarding and offboarding
- Less release friction
- Stronger governance posture
Nothing about that outcome is theoretical. It is the natural result of replacing scattered trust workflows with deliberate systems.
Signs Your Team Has Outgrown Its Current Approach
Most organizations do not need a breach to know they have a secrets problem.
The signals usually appear earlier:
You are unsure where some production credentials are stored.
A release was delayed because someone could not find the right token.
Old credentials still exist because nobody wants to break anything.
New engineers take too long to get access.
Offboarding requires detective work.
Different teams use different methods for handling secrets.
Nobody can confidently list all critical credentials in production.
These are not minor annoyances. They are symptoms of operational debt.
Why This Matters More in 2026
Infrastructure complexity is increasing, not shrinking.
Every new SaaS integration, every new microservice, every cloud account, every environment, every automation workflow, and every vendor relationship introduces additional credentials.
That means the number of secrets in a modern company often grows faster than leadership realizes.
Without a scalable operating model, the problem compounds silently.
What felt manageable at ten systems becomes painful at one hundred.
Final Thoughts
The most dangerous secrets problem is rarely the dramatic one. It is the ordinary one.
The password shared “just for today.”
The spreadsheet nobody cleaned up.
The token copied into a script to save time.
The access that was never removed.
The process everyone knows is imperfect but nobody has time to redesign.
That is how credential management breaks modern teams.
Not through one catastrophic decision, but through accumulated shortcuts that no longer fit the scale of the business.
DevOpsArk helps organizations move beyond that pattern by centralizing secrets operations, improving access governance, integrating with existing tools, and reducing the friction that drives unsafe workarounds in the first place.
Because in modern infrastructure, secrets are not just security assets.
They are operational assets.
And they deserve to be managed that way.
- access control
- api key security
- aws secrets manager
- ci cd secrets
- Cloud Security
- compliance and audit
- credential management
- credential sprawl
- DevOps Security
- DevSecOps
- enterprise secrets management
- hashicorp vault integration
- kubernetes secrets
- role based access control
- secret governance
- secret rotation
- secrets in spreadsheets
- secrets management
- secure software delivery
- shared passwords risk
Recent Posts
- Secrets in Spreadsheets? Why Credential Management Still Breaks Modern Teams
- SSH Access Chaos: Why Public Server Access Is a Security Nightmare in 2026 (And How Modern Teams Fix It)
- SSL Expired Again? Why Certificate Management Still Breaks Businesses in 2026 (And How to Finally Fix It)
- Multi Cloud Management: Why It Is More Complex Than You Think
- Release Management in DevOps: Why It Still Slows Everything Down