SSH Access
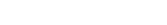
Chaos: Why Public Server Access Is a Security Nightmare in 2026 (And How Modern Teams Fix It)
Introduction There is a pattern that repeats itself across
thousands of engineering organizations. A company modernizes its
Introduction
There is a pattern that repeats itself across thousands of engineering organizations.
A company modernizes its CI/CD pipelines, migrates workloads to the cloud, adopts containers, implements observability, improves identity management, and begins discussing zero-trust security. On paper, the infrastructure strategy looks modern and mature.
Then someone runs a routine external scan and discovers multiple production servers with public IP addresses exposing SSH to the internet.
That contradiction is more common than most teams want to admit.
For many organizations, public SSH exposure is not the result of negligence. It is usually the result of gradual growth. A server needed temporary administrative access. A firewall rule was added. A bastion host was created later. New environments inherited old patterns. Access exceptions accumulated. Contractors needed temporary credentials. Multi-cloud expansion introduced inconsistent workflows. What started as a practical shortcut slowly became a permanent operating model.
The problem is not SSH itself. SSH remains one of the most trusted and effective protocols for secure remote administration. The real issue is the architecture surrounding it: public exposure, unmanaged credentials, fragmented access controls, poor auditability, and operational processes that do not scale.
In 2026, server access should be secure, governed, observable, and simple to operate. Yet many teams are still managing it through legacy patterns that create avoidable risk and unnecessary complexity.
This article explores why public server access becomes a security nightmare, what it costs organizations in practice, and how DevOpsArk helps modernize server operations through secure browser-based access, centralized management, activity tracking, and integrated provisioning workflows.
What Public Server Access Looks Like in the Real World
In theory, server access is straightforward. Administrators need a secure way to connect to infrastructure for deployments, debugging, maintenance, incident response, and system operations.
In practice, many environments evolve into something far messier.
A typical model may include:
- Linux servers with public IP addresses
- SSH exposed on port 22
- IP allowlists for office networks or engineer home IPs
- Shared private keys stored in password managers
- Bastion hosts for selected environments
- VPN requirements for some networks but not others
- Manual onboarding through tickets or chat requests
- Inconsistent logging across clouds and data centers
- Emergency access exceptions that remain permanently enabled
Each individual decision may appear reasonable. The problem emerges when these decisions accumulate across dozens or hundreds of servers.
What once felt manageable becomes difficult to secure, difficult to govern, and difficult to operate.
Why Public SSH Access Becomes a Security Nightmare
Public Exposure Increases Attack Surface Immediately
The moment an administrative interface becomes reachable from the public internet, it enters the threat landscape.
Attackers continuously scan IPv4 and cloud ranges looking for exposed services. Public SSH endpoints are among the most commonly probed because they provide a direct path to privileged infrastructure if authentication controls fail.
Common attack patterns include:
- Password brute-force attempts
- Credential stuffing using leaked credentials
- Enumeration of weak configurations
- Exploitation of outdated software
- Reconnaissance for lateral movement opportunities
- Targeting of forgotten or poorly monitored systems
Even if your organization uses key-based authentication and disables passwords, public exposure still creates noise, defensive overhead, and unnecessary risk.
Security teams are forced to monitor and defend a surface area that does not need to exist in the first place.
Credential Sprawl Becomes Inevitable Without Centralized Access Design
As environments grow, access management often shifts from policy-driven governance to convenience-driven workarounds.
This is where credential sprawl begins.
You may discover:
- Shared SSH keys used by multiple engineers
- Old contractors retaining access after projects end
- Keys copied across environments for speed
- Personal keys added directly to authorized_keys files
- No inventory of which users can access which systems
- Emergency credentials never rotated after incidents
These problems rarely appear all at once. They emerge gradually and silently.
From a security perspective, credential sprawl is dangerous because it reduces accountability. When multiple people share the same access path, it becomes harder to prove who did what, when, and why.
From an operational perspective, it creates hidden dependencies. Teams become reliant on access patterns that nobody formally owns.
Bastion Hosts Solve Some Problems While Creating Others
Bastion hosts are often introduced as a response to public SSH exposure. Instead of exposing every server, teams expose a controlled jump host and route administrative traffic through it.
That can be a meaningful improvement, but it is not cost-free.
A bastion host introduces its own operational responsibilities:
- OS patching and hardening
- MFA integration
- Session logging configuration
- High availability planning
- Capacity management during incidents
- Access lifecycle administration
- Network rule maintenance
- Monitoring and alerting
- Backup and recovery planning
In smaller teams, the bastion frequently becomes “that one system only one engineer understands.”
At that point, the organization has not eliminated complexity. It has concentrated complexity into a different place.
Access Friction Slows Engineering Velocity
Security controls should reduce risk without unnecessarily blocking legitimate work.
Unfortunately, many server access models create friction at exactly the wrong moments.
Consider common scenarios:
- A developer needs urgent log access during a production incident
- A platform engineer needs to patch a degraded node
- A release engineer needs to validate a deployment issue
- A database administrator needs emergency maintenance access
- A contractor needs time-bound access to a staging environment
If each request requires VPN troubleshooting, firewall changes, manual approvals, bastion coordination, or waiting for someone with privileged credentials, delivery speed suffers.
During incidents, this friction becomes expensive. Minutes matter when systems are degraded. Slow access processes extend recovery time.
Lack of Visibility Creates Audit and Investigation Pain
One of the biggest weaknesses in traditional SSH models is incomplete observability.
Many organizations cannot quickly answer basic governance questions such as:
- Who accessed production last week?
- Which user logged into this server during the outage?
- Was that access approved?
- What commands were executed?
- Which accounts still have active access?
- When was access last reviewed?
Without centralized visibility, incident investigations slow down and compliance audits become manual evidence-gathering exercises.
This is not just an inconvenience. It increases response time, increases audit effort, and weakens organizational trust in operational controls.
Why This Is Not Just a DevOps Problem
Server access architecture affects far more than infrastructure engineers.
Security Teams
Need reduced attack surface, stronger identity controls, and evidence of administrative activity.
IT Operations Teams
Need reliable access workflows that work consistently across environments.
Engineering Managers
Need teams to resolve issues quickly without bypassing controls.
Compliance and Governance Teams
Need traceability, policy enforcement, and reviewable records.
Business Leadership
Need uptime, continuity, and confidence that critical systems are protected.
Poor server access design becomes an organization-wide drag, not just a technical inconvenience.
The Hidden Cost of Outdated Access Models
Public SSH exposure and fragmented access workflows create costs that rarely appear in obvious budget reports.
Engineering Time Is Consumed by Access Management
Highly skilled engineers spend time:
- Managing keys
- Updating firewall rules
- Troubleshooting VPN issues
- Handling access tickets
- Rotating credentials manually
- Reconstructing access events after incidents
This is time not spent on automation, reliability, product delivery, or strategic improvements.
Security Operations Become Reactive
When access controls are fragmented, security teams must compensate through increased monitoring, more exceptions, and more manual review.
That is expensive and difficult to sustain.
Incidents Take Longer to Resolve
During outages, organizations should focus on diagnosis and remediation. Instead, many teams first struggle with who can access what and how.
Access friction directly increases mean time to recovery (MTTR).
Growth Magnifies Weak Design
A process that feels tolerable with five servers often collapses with fifty. At enterprise scale, inconsistent access models become operational debt.
Why “We Already Use a VPN” Is Not a Complete Strategy
Many organizations assume a VPN solves the server access problem because it places users “inside the network.”
A VPN may reduce exposure, but it does not automatically solve:
- Fine-grained authorization
- Per-server access governance
- Activity tracking
- Credential lifecycle management
- Centralized approvals
- Cross-cloud consistency
- User experience complexity
- Temporary contractor access
- Audit evidence generation
Network access and server access are related, but they are not the same control layer.
Modern access models need both connectivity and governance.
What Modern Server Access Should Look Like in 2026
A mature server access model should provide:
- Minimal public exposure
- Identity-based access controls
- Centralized permission management
- Time-bound or scoped access where needed
- Consistent workflows across cloud and on-prem
- Visibility into administrative activity
- Fast access during incidents
- Clean onboarding and offboarding
- Scalable operations as environments grow
This is where platform-driven approaches outperform manually stitched processes.
How DevOpsArk Solves Server Access Chaos
DevOpsArk approaches server access as an operational capability that should be secure, manageable, and scalable from day one.
Instead of relying on exposed public SSH endpoints, scattered credentials, and multiple disconnected tools, teams can manage servers through a unified platform model.
Secure Browser-Based Bastion Access
DevOpsArk provides browser-based bastion access that allows authorized users to connect to servers through a managed interface.
This significantly improves operational simplicity while helping reduce dependence on traditional public-access models.
Practical benefits include:
- Reduced reliance on exposed internet-facing SSH access
- Faster access without complex local client setup
- Consistent workflows for distributed teams
- Better control over how administrative access is delivered
The goal is not merely remote access. It is secure and manageable remote access.
Centralized Access Management
Instead of configuring access individually on every server, DevOpsArk enables centralized management of server permissions.
Organizations can manage:
- Which users access which servers
- Environment-specific restrictions
- Role changes and offboarding updates
- Standardized approval models
- Cleaner access governance across teams
Centralization reduces permission drift and lowers administrative overhead.
Activity Tracking and Operational Visibility
Access without visibility creates blind spots.
DevOpsArk includes activity tracking so organizations gain better insight into server access events and operational behavior.
This supports:
- Faster incident investigations
- Stronger accountability
- Easier internal reviews
- Better audit readiness
- Greater confidence in production operations
When a change happens during a critical event, teams should not need guesswork to understand access history.
Multi-Cloud Server Provisioning and Management
Server operations begin before access.
DevOpsArk also supports provisioning workflows across providers such as:
- AWS
- GCP
- DigitalOcean
With instance and network selection built into workflows, teams can move from provisioning to management in a consistent operational model rather than stitching together multiple tools after deployment.
Operational Simplicity at Scale
The most important long-term benefit is reduced complexity.
As infrastructure grows, DevOpsArk helps organizations avoid tool sprawl and access fragmentation by combining provisioning, secure connectivity, and visibility in one platform.
That means:
- Fewer moving parts
- Fewer manual processes
- Lower training overhead
- Cleaner governance
- More predictable operations
Real-World Example: Before and After Modernization
Consider a growing SaaS company managing servers across AWS and an internal data center.
Before
Their environment includes:
- Public SSH on multiple production servers
- Shared keys for contractors
- A bastion maintained manually
- VPN access for some teams
- No unified activity tracking
- Delays during incidents because access must be coordinated
The organization experiences frequent friction and growing security concern.
After Using DevOpsArk
They adopt centralized server operations with browser-based access, unified permissions, and activity visibility.
Results include:
- Reduced public exposure
- Faster onboarding and offboarding
- Cleaner administrative workflows
- Better audit readiness
- Faster response during production incidents
- Lower operational stress for engineering teams
The value is not only stronger security. It is smoother daily execution.
Signs Your Current Server Access Model Needs a Rethink
Your organization may be ready for modernization if any of the following are true:
- Production servers still expose public SSH
- Access depends on shared keys
- Offboarding requires manual cleanup
- Only one engineer understands the bastion setup
- Incident response is slowed by access bottlenecks
- Audit evidence takes too long to gather
- Different teams use different access methods
- Multi-cloud environments lack consistency
- You are unsure who currently has access to critical systems
These are signals of a model that has outgrown its original design.
Best Practices for Secure Server Access
Even with the right platform, good operating discipline matters.
Minimize Administrative Exposure
Do not expose management interfaces unnecessarily.
Use Centralized Identity and Access Controls
Manage permissions consistently rather than server by server.
Eliminate Shared Credentials
Every administrative action should map to accountable access.
Maintain Activity Visibility
Operational transparency improves both security and reliability.
Standardize Across Environments
Cloud, on-prem, and staging environments should not require completely different access models.
Review Access Regularly
Permissions should evolve with team roles and organizational change.
Final Thoughts
SSH is not the problem. Legacy access architecture is.
Many organizations still carry server access models that evolved gradually through exceptions, shortcuts, and historical constraints. Over time, those models create real security exposure and measurable operational friction.
Modern teams need server access that is secure without being slow, governed without being painful, and scalable without becoming another infrastructure burden.
DevOpsArk helps organizations move toward that model through browser-based secure access, centralized permissions, activity tracking, and integrated provisioning workflows.
The result is stronger control, faster operations, lower complexity, and greater confidence in the systems that keep the business running.
If server access still feels chaotic in your environment, the issue may not be SSH. It may be everything built around it.
Recent Posts
- Secrets in Spreadsheets? Why Credential Management Still Breaks Modern Teams
- SSH Access Chaos: Why Public Server Access Is a Security Nightmare in 2026 (And How Modern Teams Fix It)
- SSL Expired Again? Why Certificate Management Still Breaks Businesses in 2026 (And How to Finally Fix It)
- Multi Cloud Management: Why It Is More Complex Than You Think
- Release Management in DevOps: Why It Still Slows Everything Down