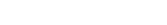
SSL Expired
Again? Why Certificate Management Still Breaks Businesses in 2026 (And How to Finally Fix It)
There is a particular kind of dread
that hits when your phone lights up at
There is a particular kind of dread that hits when your phone lights up at 2 AM with a Slack message that just says: “The site is down. Browser is throwing a security warning.”
You already know what happened. You do not even need to open the dashboard to confirm it. Somewhere in your infrastructure — probably something nobody has touched in eighteen months — an SSL certificate quietly crossed its expiration date, and now your customers are staring at a big red warning screen telling them your connection is not private.
This is not a rare story. This is Tuesday for a lot of engineering teams in 2026. And it keeps happening because SSL certificate management — the actual discipline of tracking, renewing, and deploying certificates across your entire infrastructure — remains one of the most underestimated operational risks in modern engineering.
What makes it so frustrating is that SSL and TLS certificates are not new, mysterious technology. They have been around for decades. The tooling is mature. Automation exists. And yet, certificate-related outages keep happening — at startups, at enterprises, at companies that otherwise have excellent DevOps practices and genuinely smart infrastructure teams.
The problem was never the certificate itself. The problem is everything around the certificate — the visibility, the ownership, the renewal workflows, the scattered environments. And that is exactly what this article is going to unpack.
What SSL Certificate Management Actually Means (And Why It Is Bigger Than You Think)
Most people hear “SSL certificate management” and think: renew the cert before it expires. Done.
That is a bit like saying “car maintenance” means checking your tire pressure once a year. Technically true, profoundly incomplete.
SSL and TLS certificate management covers the entire lifecycle of every certificate your organization depends on. That means issuing them, deploying them to the right systems, monitoring their expiration dates continuously, rotating them when something goes wrong, managing the certificate authorities that sign them, keeping records for compliance audits, and doing all of this consistently across environments that were probably never designed to work together.
In a small company running a single web application, this is genuinely manageable. One or two certificates, one renewal per year, done.
In a company that has grown — multiple products, a microservices architecture, Kubernetes clusters, AWS workloads, on-premises servers, internal tools, partner APIs, staging environments — certificate management has quietly become a major operational discipline that most organizations are still treating like a footnote.
That gap is where outages live.
Why SSL Certificates Matter More in 2026 Than They Did Five Years Ago
You might think that as infrastructure has become more automated and cloud-native, certificate problems would naturally get easier to manage. In some ways, yes. In others, the problem has actually gotten significantly harder — because there are simply far more certificates to keep track of.
Every microservice that communicates over HTTPS needs a certificate. Every Kubernetes ingress resource needs a certificate. Every internal dashboard, every admin panel, every API endpoint used by a third-party integration — all of it depends on valid, trusted certificates to function. The surface area has exploded.And the stakes are higher too.
Customer trust is immediate and fragile. When a browser displays a “Your connection is not private” warning, users do not think “oh, probably just a certificate issue.” They think “this site is not safe” and they leave. The confidence damage happens in the first three seconds, and some of it does not come back even after you fix the underlying problem.
APIs do not forgive expired certificates. A browser will at least show a warning and let a stubborn user click through. APIs just fail. If a payment integration, an authentication service, or an internal automation pipeline hits an expired certificate, it does not degrade gracefully — it stops. Entirely.
Compliance frameworks have gotten stricter. Whether you are working within SOC 2, ISO 27001, PCI DSS, or any number of regional data protection frameworks, certificate hygiene is increasingly part of what auditors check. Undocumented certificates, missed renewals, and informal processes create real compliance exposure.
Zero-trust security architectures depend on certificate-based authentication. If you are building toward a zero-trust model — and most serious engineering organizations are — certificates are not just for encrypting web traffic. They are part of how services verify each other’s identity. A lapsed certificate in that context is not an inconvenience. It is a security gap.
The Real Reasons Certificate Management Keeps Failing (It Is Not What You Think)
Here is the thing about certificate failures: they almost never happen because engineers do not understand how SSL works. The people who get paged at 2 AM absolutely know what a certificate is and how to renew one.
The failures happen because of process problems, not knowledge problems. Specifically, these five patterns show up over and over again.
You Cannot Manage What You Cannot See
The first and most fundamental problem is visibility — or rather, the lack of it.
In a company that has been building and shipping for a few years, certificates end up scattered across a remarkable number of places. Some live in AWS Certificate Manager. Some are deployed directly to NGINX configurations on EC2 instances. Some are managed through Kubernetes secrets and cert-manager. Some exist in a cloud load balancer configuration that someone set up eighteen months ago and has not been touched since. Some are stored as files on a legacy server running an internal tool that three people in the organization use and nobody fully owns.
When you do not have centralized visibility across all of those locations, you are essentially flying blind. The certificate that expires is never the one you were watching. It is always the one you forgot existed.
Spreadsheets and Calendar Reminders Are Not a Monitoring Strategy
Ask ten engineering teams how they track certificate expiration dates, and at least four of them will tell you some version of the same answer: a shared spreadsheet, a recurring calendar reminder, or both.
This works until it does not. Spreadsheets get out of date the moment someone adds a new certificate without updating the sheet. Calendar reminders get dismissed or missed during a busy period. The person who originally set up the reminder leaves the company, and their calendar disappears with them.
These are not failures of diligence. They are structural failures — manual systems trying to manage a problem that has grown beyond what manual systems can reliably handle.
Nobody Is Quite Sure Who Owns What
Here is a scenario that plays out in more organizations than anyone wants to admit: an alert fires because a certificate on an internal service is expiring in 72 hours. The on-call engineer acknowledges the alert and immediately opens a Slack thread asking who owns that service. Four people are tagged. Two of them respond. None of them are sure whether they have access to renew the certificate or where it is even deployed.
Unclear ownership is arguably the most dangerous failure mode because it creates delay at exactly the moment when speed matters most.
Different Environments, Different Processes, Zero Consistency
Production certificates might be managed through an automated workflow with Let’s Encrypt. Staging certificates might be self-signed and manually updated whenever someone complains. Internal tools might use certificates from an enterprise CA that requires a ticket submission and a three-day wait.
When every environment has its own certificate process — or no consistent process at all — the cognitive load of managing it all adds up fast. And inconsistency breeds mistakes.
Internal Certificates Are the Invisible Risk
Public-facing websites get attention because when they break, users notice immediately. Internal certificates — the ones protecting your admin dashboards, your internal APIs, your development tools, your logging infrastructure — often go unmonitored until they fail. And when they fail, they tend to break things in ways that are genuinely confusing, because people do not expect internal tools to throw certificate errors.
What Actually Happens When a Certificate Expires (The Full Cost Nobody Talks About)
The technical consequence of an expired certificate is simple: connections fail. The business consequence is considerably more complex.
Revenue impact starts immediately. If an expired certificate takes down a checkout flow, a customer portal, or a SaaS dashboard, you are not just losing traffic — you are losing customers who were in the middle of a purchase or a workflow. Even a two-hour outage during peak usage hours can represent significant lost revenue, particularly for transactional businesses.
Engineering capacity gets consumed. Certificate incidents do not get resolved at a leisurely pace. They are treated as emergencies, which means engineers drop whatever they were working on — planned features, technical debt, other infrastructure work — to diagnose, fix, redeploy, and validate. A problem that takes an hour to resolve might consume four or five hours of high-context engineering time by the time you account for the investigation, the coordination, and the post-incident review.
Customer support volumes spike. Users who encounter browser warnings or broken integrations do not always know what is happening. They know something is wrong, and they contact support. That creates queuing, delays, and a lot of conversations that amount to “we are working on it, please bear with us” — which is not a great customer experience under any circumstances.
The reputational damage is underappreciated. A customer who hits a security warning on your domain does not just have a bad experience in that moment. They remember it. They might tell someone else. In B2B contexts especially, where trust is foundational to the relationship, a certificate incident can create doubt that takes months to fully dispel.
Compliance exposure is real. An expired certificate is not just an operational problem — it can be a compliance problem too. Depending on your regulatory environment, certificate-related failures may need to be documented, reported, and explained to auditors. Informal processes that could not prevent the failure become evidence of a broader governance issue.
Why “We Will Just Automate Renewals” Is Only Half the Solution
Let’s Encrypt changed the game when it launched. Free certificates, automated renewal via ACME, no more annual renewal fees — for public-facing web services, it genuinely solved a large part of the certificate management problem.
But a lot of organizations adopted certificate automation for their public services and called it done. The problem is that automation for renewal does not solve the underlying challenges of visibility, deployment consistency, internal certificate management, or multi-environment coordination.
You can have perfectly automated Let’s Encrypt renewals for your customer-facing domains and still have an internal service running on an expired certificate that nobody knew about. You can have renewal automation in place and still have a deployment failure that leaves a renewed certificate sitting in one system while the service that needs it is still running the expired version. You can have automation configured and still not know which certificates exist across your Kubernetes clusters, your cloud load balancers, and your on-premises servers.
Renewal is one step in the lifecycle. Certificate management is the whole thing.
How DevOpsArk Approaches Certificate Management Differently
DevOpsArk was built around a simple observation: the reason certificate problems persist is not that good certificate tooling does not exist. It is that most organizations manage certificates through a collection of disconnected tools, ad hoc processes, and institutional knowledge that lives in people’s heads rather than in documented systems.
The solution is not to add another tool to the pile. It is to centralize the entire certificate lifecycle — visibility, issuance, renewal, deployment, monitoring — into a single operational platform.
Here is what that looks like in practice.
A Single Inventory Across Every Environment
The first thing DevOpsArk gives you is something deceptively simple and deeply valuable: a complete, centralized view of every certificate your organization uses.
This sounds obvious. It is surprisingly rare.
Instead of hunting through AWS consoles, Kubernetes cluster configs, server directories, and shared spreadsheets to figure out what certificates you have and where they live, you get a unified inventory. Every certificate, every environment, every expiration date, visible from one place.
The impact of this alone is significant. Forgotten certificates get found before they expire. Ownership gets established before it is urgent. Audits that used to require manual evidence gathering become a matter of pulling a report.
Automated Renewal That Actually Covers Your Stack
DevOpsArk supports automated renewal workflows, including Let’s Encrypt via ACME, designed to work across the kinds of mixed, heterogeneous infrastructure that real organizations actually run — not just the neat, idealized single-server setup that most automation examples are built around.
The goal is to take the renewal process out of people’s to-do lists entirely for the vast majority of certificates. Because a renewal that happens automatically and correctly is a renewal that cannot be forgotten, delayed, or dropped during a busy sprint.
Public and Private Certificates, Managed Together
One of the underappreciated complexity sources in enterprise certificate management is that public certificates and private certificates follow completely different trust models and often completely different workflows.
Public certificates — the ones used for customer-facing websites, APIs, and portals — need to be trusted by browsers and external clients. Private certificates — the ones used for internal dashboards, service-to-service communication, and corporate applications — need to be managed through an internal CA that your organization controls.
DevOpsArk handles both, which means you are not managing two separate certificate programs with two separate tools and two separate mental models. Your public certificates and your private PKI infrastructure are managed through the same platform, with the same visibility, the same monitoring, and the same operational workflows.
Kubernetes Certificate Deployment
If you are running containerized workloads in Kubernetes, you already know that certificate management in that environment has its own set of complexities — ingress resources, cert-manager integration, secret management, multi-cluster coordination.
DevOpsArk supports deployment to Kubernetes ingress environments, which is genuinely important for teams managing frequent deployments across multiple clusters. A certificate renewal that does not automatically propagate to the right Kubernetes secrets is a renewal that has not actually fixed the problem.
AWS ACM Integration
Many organizations use AWS services — Application Load Balancers, CloudFront distributions, API Gateway — that depend on certificates managed through AWS Certificate Manager. DevOpsArk integrates with ACM workflows so that your cloud-native certificate management is part of the same unified operational picture, rather than a separate silo that falls outside your central visibility.
Expiry Monitoring That Tells You Before Users Do
The difference between proactive monitoring and reactive monitoring is the difference between renewing a certificate with three weeks to spare and getting paged at midnight because the cert expired six hours ago.
DevOpsArk’s expiry tracking surfaces upcoming renewals well before they become urgent, so your team can act on the information during planned work rather than in emergency mode. The goal is to make certificate expiration something you read about on a Monday morning dashboard review, not something you find out about from a customer complaint.
Manual Upload for Existing Certificates
Not every certificate in your organization comes from Let’s Encrypt or an automated CA. Enterprise certificate providers, third-party vendors, and legacy systems often produce certificates that need to be manually imported and managed. DevOpsArk supports manual uploads precisely so that you do not have to run two parallel systems — one for the certificates you can automate and one for the certificates you cannot.
What the Before and After Actually Looks Like
Consider a mid-size technology company managing roughly forty to fifty certificates across their infrastructure — public websites, internal tools, staging environments, a Kubernetes-based microservices platform, several AWS-hosted services, and a handful of legacy applications.
Before centralizing their certificate management, the situation looked like this: renewal dates were tracked in a spreadsheet that was last updated four months ago. Three different team members had knowledge of specific certificate workflows, but no single person had visibility across the whole picture. Kubernetes certificates were managed through cert-manager but not monitored centrally. AWS ACM certificates existed in a separate workflow entirely. Internal certificates were renewed manually, usually after someone noticed a tool was throwing errors.
In the previous twelve months, they had experienced two certificate-related incidents — one that took down a customer-facing portal for three hours, and one that broke an internal deployment pipeline for most of an afternoon. Both were preventable.
After moving to a centralized platform, the same team has a complete inventory updated continuously. Renewal workflows run automatically for the certificates that support automation. Expiry alerts surface upcoming renewals weeks in advance. The Kubernetes and ACM certificates are visible in the same dashboard as the rest of the infrastructure. And when a new certificate is added anywhere in the stack, it goes into the central inventory immediately rather than becoming an invisible risk.
The engineering time that used to go into certificate firefighting now goes into planned work. That is not a small thing.
Signs That Your Current Certificate Process Is Due for a Rethink
You do not need to wait for an incident to know whether your current approach is working. Here are the patterns that tend to show up before the eventual outage:
Your renewal tracking lives in a spreadsheet or a calendar, and you are not fully confident it is up to date. Only one or two people in your organization can actually walk through the certificate renewal process for a given service. You have discovered expired certificates on internal tools that nobody had flagged. Your Kubernetes certificates and your cloud certificates follow completely different workflows managed by completely different people. The last time an auditor asked about your certificate inventory, someone had to spend a day pulling it together manually. Certificate renewals occasionally create unplanned work during otherwise quiet periods. You are not entirely sure how many certificates your organization is currently running.
If several of these resonate, the underlying issue is not that your team is doing something wrong. It is that the process has outgrown the tooling.
Building a Certificate Management Practice That Actually Scales
The right tooling matters, but so does the operational practice around it. Here is what sustainable certificate management looks like for organizations that have gotten this right.
Centralized visibility is non-negotiable. If you cannot see all of your certificates — across environments, across cloud providers, across public and internal systems — in one place, you are managing by memory and luck. That is not a sustainable position as your infrastructure grows.
Ownership needs to be explicit and documented. Every certificate should have a designated owner — a team, a service, a person — that is responsible for it. When that is clear before the alert fires, response time drops dramatically.
Automate everything you can, and know what you cannot. Let automation handle the routine renewals for the certificates it can reach. Understand clearly which certificates require manual steps and make sure those are monitored just as rigorously as the automated ones.
Monitor proactively and set generous lead times. A thirty-day expiry warning gives you time to act without urgency. A seven-day warning means you probably need to drop something to address it. A one-day warning means you are already in incident mode. Set your monitoring thresholds to give yourself real working time.
Treat internal certificates like first-class citizens. The internal tools and services that your team depends on every day deserve the same certificate hygiene as your customer-facing systems. Outages on internal infrastructure affect productivity, deployment pipelines, and development velocity in ways that compound quickly.
Build certificate review into your regular operational cadence. A monthly or quarterly review of your certificate inventory — checking for changes, verifying ownership, confirming that automation is running correctly — catches problems before they become incidents.
The Bottom Line
SSL certificates are not going away. If anything, the shift toward zero-trust security models, encrypted service meshes, and certificate-based service authentication means that the number of certificates your organization depends on is going to keep growing.
The question is not whether you need to manage them well. The question is whether you build the processes and tooling to do it proactively, or whether you keep learning about certificate problems from user complaints and midnight pages.
If your current approach involves spreadsheets, tribal knowledge, and reactive monitoring, that is not a reflection of your team’s competence — it is a reflection of the fact that certificate management complexity has grown faster than most organizations have adapted their processes to keep up.
DevOpsArk centralizes the certificate lifecycle — inventory, issuance, renewal, deployment, monitoring — into a platform designed for the kind of distributed, multi-environment infrastructure that modern engineering teams actually operate. The result is not just fewer outages. It is a fundamentally less stressful, more scalable way to keep your infrastructure’s trust layer intact.
Your certificates should be one of the quietest, most boring parts of your operations. With the right foundation in place, they can be.
- acme certificate renewal
- api certificate management
- aws acm certificate management
- browser security warning
- certificate compliance
- certificate expiry tracking
- certificate governance
- certificate inventory
- certificate lifecycle management
- certificate operations
- certificate renewal automation
- certificate rotation
- certificate visibility
- cloud certificate management
- DevOps Security
- devopsark certificate management
- devopsark ssl
- DevSecOps
- enterprise ssl management
- expired ssl certificate fix
- https certificate management
- Infrastructure Security
- internal certificate management
- kubernetes ingress tls
- kubernetes ssl certificates
- lets encrypt automation
- multi cloud certificate management
- private ca management
- proactive certificate monitoring
- public ssl certificates
- secure digital trust
- ssl best practices
- ssl certificate automation
- ssl certificate expiration
- ssl certificate management
- ssl certificate renewal
- ssl management platform
- ssl monitoring
- ssl outage prevention
- tls certificate management
- tls monitoring
- website security certificates
- zero trust security
Recent Posts
- SSL Expired Again? Why Certificate Management Still Breaks Businesses in 2026 (And How to Finally Fix It)
- Multi Cloud Management: Why It Is More Complex Than You Think
- Release Management in DevOps: Why It Still Slows Everything Down
- Why DevOps Security Still Breaks in Production (Even After DevSecOps)
- Reducing DevOps Cognitive Load with DevOpsArk Platform